Advertisement
If you have a new account but are having problems posting or verifying your account, please email us on hello@boards.ie for help. Thanks :)
Hello all! Please ensure that you are posting a new thread or question in the appropriate forum. The Feedback forum is overwhelmed with questions that are having to be moved elsewhere. If you need help to verify your account contact hello@boards.ie
Hi all! We have been experiencing an issue on site where threads have been missing the latest postings. The platform host Vanilla are working on this issue. A workaround that has been used by some is to navigate back from 1 to 10+ pages to re-sync the thread and this will then show the latest posts. Thanks, Mike.
Hi there,
There is an issue with role permissions that is being worked on at the moment.
If you are having trouble with access or permissions on regional forums please post here to get access: https://www.boards.ie/discussion/2058365403/you-do-not-have-permission-for-that#latest
There is an issue with role permissions that is being worked on at the moment.
If you are having trouble with access or permissions on regional forums please post here to get access: https://www.boards.ie/discussion/2058365403/you-do-not-have-permission-for-that#latest
So you want to JTAG your xbox360? (POST 248 FOR xeBuild/16197 TUT)
-
31-10-2010 4:55pm#1I get a few private messages and there are plenty of posts here on the forum about the xbox 360 JTAG. With that in mind, here's a condensed version of what you need to know, and what you need to do to get up and running with your very own JTAG.
Please note that a more thorough/complete guide is available here.
Can my console be JTAG'd?
The key to the JTAG is the version of the console's 2nd level bootloader (CB). Certain bootloaders are vulnerable to exploitation, others are not. A massive indicator as to the eligibility of the console for the JTAG is the dashboard version you are running. Go to the System Settings menu, then Console Settings and then System Information. You will see the "Dashboard version" on the right. You need a dashboard version of 2.0.7371 or lower before you begin. If the dashboard version is higher (e.g. 2.0.8955, 2.0.9199 etc) then you cannot JTAG.
Following the dashboard check, you need to check the console's manufacturing date/service date which is printed on a sticker above the A/V or HDMI ports. Microsoft began updating the bootloader to an unexploitable version on new consoles in June 2009. So if your console has a manufacturing date or service date before June 2009 (in addition to the dashboard version of 2.0.7371 or lower) then it's almost a certainty that you can JTAG.
There are a few exceptions to the June 2009 general rule. I have a console here that was sent to Microsoft for an RROD repair and came back with the date July 28th 2009 and it had dashboard 2.0.7371 and the old bootloader - it is JTAG'd. I also have one that came back dated August 5th 2009 with dashboard 2.0.7371 but it has the new bootloader and cannot be JTAG'd. I have consoles here with manufacturing dates of 10th June 2009 and 16th June 2009, both of which are JTAG'd. Even still, purchasing a June 2009 console for the JTAG is risky and I would strongly advise against it. If you must purchase one, purchase one with a date as early into June as you can.
I have the right dashboard version but the date is June/July 2009, what now?
There's a very high chance you cannot JTAG. The only way to be 100% sure is to read the xbox 360's memory, and use a program called 360 Flash Tool to get your 2BL (bootloader, CB) version if you took a full memory dump, or a hex editor if you took a 2MB dump.
I have the wrong dashboard version, what now?
It's the end of the road for that console. It took years to figure the first exploit out, and now that it's patched there is very little chance of finding another one. I definitely wouldn't be holding my breath. Go find another console.
Reading/Writing to the Xbox 360's NAND (memory)
Reading the 360's memory is done over LPT port or USB.
LPT is an ancient standard and many newer computers (and laptops) do not have LPT ports. You need what's known as a "native" port, that is one that's built into the laptop or motherboard. There may be sporadic reports of somebody buying an LPT expansion card and that working but it is taking a risk, it probably won't work. LPT is slow, much slower than USB. A 16mb memory dump over LPT takes approximately 40 minutes. For arcade consoles (256MB/512MB internal storage) you need to dump the first 64MB, which will take 3 hours over LPT. LPT is also prone to problems caused by poor soldering, interference and device polling. That isn't to say it can't be done, my first JTAG was performed over LPT.
USB is much faster than LPT. Dumping with a PIC18F2555 board with a 12MHz crystal and a 64MB nand takes 35-40 minutes and a 16MB nand takes 6 minutes. There are faster solutions out there, like the Nand-X by Xecutor that can dump a 16MB nand in around 2 minutes. USB is less affected by interference and is generally less fussy than the LPT reader in a "It just works" kinda way.
Personally I would recommend USB, though that usually involves a pricey enough sum to buy the USB reader/flasher - €25-€30, or more in the case of the Nand-X. You can try build your own PIC-based USB flasher, but I've tried and failed, as have a few others on here - maybe we're crap builders
The guide I linked to has information about LPT/USB readers and how to build them.
There are two headers on the xbox 360 motherboard, they are labelled J1D2 and J2B1. You need to solder 4 wires to J1D2 and 2 wires to J2B1, no matter what method you choose. In addition to this, you need a ground wire which can be taken from any ground point. I choose to use the little thin stems from the outside of any xbox 360 connector port (e.g. the AV port, the hard drive port, the memory unit port). This is because heating them up to flow the solder is much easier than heating other suggested ground points (for example J1D2.6, or J2B1.12).
Up-close look at J1D2, complete with numbering for the nand reader:
This is J2B1:
Here's a picture of a Falcon motherboard hooked up to my nand reader:
Nandpro
So you've hooked up a nand reader. Your next step is to get a copy of Nandpro, the latest version at the time of writing is 2.0e. Put the power plug into your console, but do not turn it on. You just want the console in standby mode.
To begin the JTAG you need to take a backup of some data off your console, including the all important keyvault.
To do this there are two ways, one is to take a dump of the first 2MB of memory, install Xellous and then take a dump of the rest by hooking up the xbox and computer with a network cable. The other is to take a full backup from your reader (highly recommended for all consoles). I'm going to go with dumping the first 2MB of the nand and checking the CB version first to see if the console is JTAGable. I'll follow with a full backup after that. If you want to try dumping the rest of the nand over HTTP (may or may not work) then go to the next section after dumping the first 2MB and the Keyvault, you can skip the bit about dumping 16 or 64MB. If the HTTP dump doesn't work, come back here and take the full backup.
Open a command prompt (Start->Run->cmd.exe) and change directory to to wherever you extracted nandpro (e.g. "cd c:\xbox\nandpro") and type the following (replace usb: with lpt: where necessary)nandpro usb: -r2 2mb_dump1.bin
This will use USB to read the first 2MB of your nand into the file 2mb_dump1.bin.
If you get an error about "Could not detect flash controller" there is a problem with your reader so check your soldering with a multimeter, ensure you have the right drivers installed for USB etc etc. This isn't a troubleshooting guide so start your own thread here on the forum and we'll try help, or check out the big guide at the top of the post. If you have any bad blocks within the first 50 blocks of your nand when reading it, then you may have issues getting Xellous working so create your own thread and we'll look at your problem. Make sure to create a thread if you've got a bad block at block #1 (your Keyvault). If you have more than 32 bad blocks, something is wrong with your reader.
What you should see is something like the following image which is from my first JTAG (using LPT):
Keep an eye on the FlashConfig value, valid ones are : 01198010, 00AA3020 and 00023010. Google any other value to see if it's common or a problem. You don't want to take a botched dump.
Run the same command again changing dump1 to dump2. Do not unplug the console between dumps. Now you've two separate reads of the nand. Next, run the following command:fc 2mb_dump1.bin 2mb_dump2.bin
This will compare the two files to each other. They need to be the same. FC should state no file differences found. If they are not the same, and FC reports a few changes between the files then dump a third time, checking your wires etc for problems. You need matching dumps. If they don't match, re-check your wires and reader and dump again until you have two (or ideally 3) matching dumps. That way you can be pretty sure you got a valid dump.
Open up a hex editor and then open up your 2MB nand dump. Press the find button, make sure ASCII is selected, and type CB. It should bring you to line number 8400 where there first two numbers are 43 42 (which is CB in Hex). Take note of the next two numbers. In the following picture, they are 1a 43: .
.
Open up the Windows Calculator (Start->Run->calc.exe) then press View->Programmer. Make sure the radio button for Hex is pressed, then type in the numbers you have (no space required). Then click DEC to convert it into decimal. 1a43 converts to 6723 in decimal, which is a vulnerable CB.Exploitable CB versions wrote:Xenon: 1921 or lower is Exploitable (exception: 8192 IS EXPLOITABLE)
Zephyr: 4558 or lower is Exploitable (exception: 4580 IS EXPLOITABLE but needs falcon version of Free60)
Falcon: 5770 or lower is Exploitable
Jasper 16mb: 6712 or lower is Exploitable
Jasper Arcade (256/512): 6723 or lower is Exploitable
If your CB is not here, it isn't exploitable. Put your console back together, the dream is over. But if the show must go on...
The full backup via NANDpro
This tells nandpro to use the USB reader, -r means read so -r16 = read 16MB and xbox_backup.bin is the file it's going to read to.nandpro usb: -r16 xbox_backup1.bin
There are 3 types of memory size in use in xbox consoles, 16MB, 256MB and 512MB. Most older consoles have 16MB only, so the -r16 switch is fine. The arcade consoles need a different commandnandpro usb: -r256 xbox_backup1.bin 0 1000
Change 256 to 512MB where required. This tells nandpro to read from 0 (first block of memory to block 0x1000). The dump should be approximately 64MB in size. There is no need to dump all 256MB or 512MB of memory, anything after block 0x0FFF (i.e. 0x1000 or higher) is on-board storage, and you have already backed that up, right? :pac:
When that dump is completed, run the same command again, but change the filename to xbox_backup2.bin.
Once that's done, type the following:fc xbox_backup1.bin xbox_backup2.bin
Again, you don't want any differences between the dumps. I dump my nand 3 times to make extra sure.
Flashing Xellous
So you either have a full backup of your nand now, or you're going to try take it via HTTP once you get Xellous running.
The first thing you need to do is read your Keyvault from the nandnandpro usb: -r1 keyvault_1.bin 1 1
This will read your keyvault (which is located at block 1, and ends at block 1, hence the 1 1 at the end of the command so don't forget this). Again, dump it a second time to a different file and compare them. Make sure they're the same.
Now you need to grab Xellous. The file you want depends on your motherboard revision. If you don't know what it is, then consult this image
I'm putting the links here, the code is not copyrighted by Microsoft so it's fair game. Other mirrors are in the guide.
Xenon - Mirror 1
Falcon/Zephyr/Opus/Jasper - Mirror 1
Extract xenon_hack_xellous.bin or <falcon/zephyr/opus/jasper>.xellous.smc.bin to the nandpro directory.
Rename it to free60.bin for simplicity. You're now going to write it to your console.nandpro usb: -w2 free60.bin 0
The above command can be interpreted as write via USB, 2MB of data from free60.bin to the nand starting at block 0. Make sure this is the command you're using, only changing USB to LPT where necessary.
Once nandpro has flashed Xellous, you need to write your keyvault to the nand or it won't boot.nandpro usb: -w1 keyvault_1.bin 1 1
This command can be interpreted as write (with a limit of 1MB maximum) keyvault_1.bin to the nand, starting at block 1 and only write 1 block (which is all the keyvault is, one block).
Now that it's done you can desolder your reader. I don't, just in case I run into a problem that might mean flashed back the original nand for testing but you can do it if you want because if this works you're finished with the nand flashing
Either way, take out the power plug and disconnect the reader from your computer, it's time to solder the actual JTAG
The JTAG
All this mucking around with the nand doesn't make stuff happen. You need to solder a few more wires to get the code you've just flashed to the nand to actually work. This is the heart of the JTAG, the wiring that unleashes the xbox.
For the Xenon model, you will need 2x1N4148 diodes or 2xSchottky BAT41 diodes and 3 wires. For all other models you will need 7 wires, 2x10k resistors and 2x2N3904 NPN transistors.
Xenon
The diode should be soldered directly to the motherboard at J1F1.3 and J1F1.4 with the thick black line on it nearest the board. Do not solder wire->diode->wire, this may cause problems.
Others:
Click here for bigger image. The 2N304 transistor has a flat back with a curved front as in the small image. With the legs facing you and the transistor on it's back the legs go C, B, E.
Please take special note of the location of AUD_CLAMP. There is another transistor (Q2N3) to the right of Q2N1, you do not want to solder there so check and double-check that you're nailing Q2N1's right side leg and nothing else. The wire from Q2N1 can be run through the hole just south of it (the black hole in the image) which will bring it to the other side of the board in a much neater fashion than around the edge of the board. The blue line on J2D2 does connect pads 4 and 7, so there is a jumper wire there. I suggest all 3 wires connecting to pad 7 are twisted together, and soldered in one go with plenty of excess on the other end for trimming to length. Soldering one at a time is a pain and the last thing you want is a fleck of hot solder from the wire you just soldered there hitting your skin while you try to solder the next one.
DB1F1 is tiny and almost always has no solder on the top side. I suggest liberal use of flux and don't forget to put solder on the point before trying to solder wire to it. Apply flux, heat up the pad, apply solder, remove, wait for the pad to cool down, apply flux, apply wire, heat and apply more solder to wire & pad and you're done. Always let the pad cool down, it can be tricky but don't rush it. All of the alternative points to DB1F1 are more difficult so you really don't want to lift the pad. Also, make sure you're putting the right transistor c-leg the the right pad (1 or 2) on J2D2. Mixing up the two C-legs on J2D2 leads to an E79
Here is a picture of the above wiring in action: 15
15
Comments
-
Starting Xellous
So now that you're done soldering, double checking with the schematic, checking for shorts etc it is time to start it up. Put in the power and the AV cable, and the fan and power on the console. You should see Xellous starting up with a nice blue screen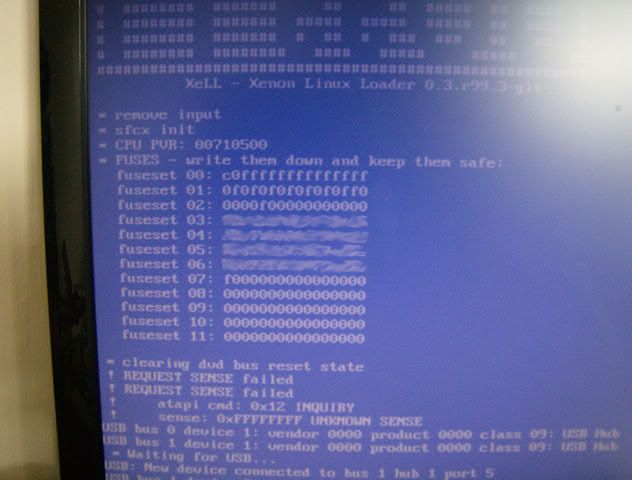
If there is any problem, double check your wires and test your parts. Honestly, most of the time is the wires or dodgy parts that cause issues.
If you only get a black screen but the tv is receiving input then make sure you've flashed your keyvault properly. If you get a blank screen and your TV is still awaiting a signal, then there are a few things you can try. First on the list is a reflash. Secondly, if you own a Big Block console (Jasper with onboard storage) you can try these Xellous files instead (Try flash xellous.jasperbb mana100.bin instead of free60.bin then flash your keyvault. If that fails, try jasper_6723_hack_for_256mb_512mb.TMS.Patched.bin and then your keyvault. If you have to use the second bin file, copy updxell.bin to a USB stick, put it in and boot into Xell to upgrade to Xellous. There is no need to do this if the first bin file works). After each reflash, remove the power to the console for 30 seconds before reconnecting it and turning it on.
After booting up into Xellous, you need to take down your CPU Key. This is the key to your console. It is unique, so keep it private and don't post it on the internet unless you want Microsoft to be aware you're raping their console! It's also very important, you can do all sorts of things with it so do keep it safe too. It's also required for the next step. The CPU key is hexademical, so the only possible values are 0-9 and A-F. There are no other letters, so there is no letter O, that's a zero.
This step is not necessary if you took a full backup already but if you want to take a backup of your nand over HTTP (which I've found to be rather unreliable myself, but many others have had success) then connect the console up to a computer with a network cable, assign your network adapter to a similar IP address to the one Xellous shows (httpd address in the above image) (e.g. 192.168.0.141 - google how to do that if you need to) and type in http://192.168.0.142 in your browser's address bar and click download beside "Raw Flash".
This can take a while, but make sure what you download is the size it's meant to be. 16MB (or 16.5mb as reported by Windows) or 256MB/512MB. There is just one more thing to do with this full backup, that is you need to restore the first 2MB of the original nand - remember, the first 2MB of that full backup you just took has Xellous in it. To do this you need Nandpro 2.0b - this is the last working version of nandpro where you can do the following command. Put rawflash.bin (or whatever you named the full backup into the nandpro 2.0b directory, and put in the dump of the first 2mb too. Then run the followingnandpro rawflash.bin: -w2 first2mb_1.bin 0
Nandpro will open rawflash.bin and write the first 2MB of first2mb_1.bin into rawflash.bin from block 0 (i.e. the start). When it's done rawflash.bin will be a full backup of what was originally on your xbox memory. Keep it safe
Verify that CPU Key
So now, one way or another, you have a backup of your entire xbox memory as it was before you messed around with it. And you have your CPU key from Xellous wrote down. Verify the CPU key with 360 Flash Tool (latest version v0.97) as follows:
Open 360 Flash Tool, Click Settings, Click Keys. Enter the CPU Key into the CPU key box. In the UserInfo box I put in the console serial number as found on the back sticker. Then Click Add-CPU Key, then click OK. Now open up your full xbox backup. You should see something like the following (I've edited out keys and other sensitive information). If you can see your DVD Key and OSIG data instead of "Bad K/V" then you've got a valid dump, and a valid CPU Key.
Freeboot
Freeboot has gotten easier to install with the invention of BestPig's Freeboot Toolbox (Don't worry, it is in English )
)
All you need is a copy of your nand backup and your CPU Key. If you're JTAGing a Xenon you're set, if you're not then you need one other file - the appropriate SMC file from the Xellous archive you downloaded earlier (i.e. Jasper.smc.bin for 16MB Jaspers, Zephyr.smc.bin etc etc). Don't forget that if you had to use that special version of Xellous for Big-Block Jaspers (by mana100) then you need to use that smc.bin file.
So fire up Bestpig's toolbox, type in your CPU key or copy it from the keys section in the 360 flash tool, check the option for updflash.bin instead of freeBOOT.bin in Destination and if you're doing a Xenon click Generate, if you're doing any other make sure to check the box for Custom Freeboot and if you're doing a Jasper make sure to also uncheck the auto-detect box and choose the right Jasper (16MB/256MB/512MB) model in the version box under the CPU key and then click Generate.
A box will pop up, asking you to open file. So find your full nand backup and double-click it. It will say something like "Jasper 16MB, CB Version xxxx - is this correct?" and you click yes after verifying the details in 360 Flash tool.
If you're on a Xenon, it will generate freeboot in a file called updflash.bin almost immediately.
If you're not then a window will pop up with a few folders - this is the temporary directory for building freeboot. You need to copy your <model-name>.smc.bin file into the data directory here, delete the existing smc.bin file and rename <model-name>.smc.bin file to smc.bin. Finally, if you are running a 256MB/512MB Jasper, you need download a file here, and copy over patches_jasper.bin from that file to the bin folder, overwriting the existing patches_jasper.bin.
Once you are done, go back to Bestpig's utlity, and click OK on the prompt there. The window will disappear and freeboot will be generated as updflash.bin in the directory where your nand file was.
Copy updflash.bin to a USB stick, put it into the console and power it on. Xellous will start, but will scan your USB stick for updflash.bin and will tell you it found an update. You have 15 second to prevent the update by turning off the console, so don't
Xellous will then read the file, this can take up to 5 minutes for slow USB sticks, and then it will flash your nand. It's incredibly fast once it gets going and when it's over you will be asked to remove the update (USB stick) and power cycle the console. So turn it off, pull the plug, wait 30 seconds and put it back in again. When you turn on the console, you should see the xbox 360 logo and be presented with the language choice screen.
Efuses - the last straw
Now that you're up and running, the last thing you want to do is accidentally update or run a game update which would flash the console but burn an efuse. When an efuse is burned, there is no way back. The burning of the efuse with the 2.0.8955 dashboard update in 2009 killed the JTAG by changing the bootloader and burning the fuse so there was no going back. Even the next update to 2.0.9199 burned another fuse, so there's no downgrading to dashboard 8955 from 9199. It really is the last thing you want to happen.
So what do you do? Well you remove the power to the efuse burning circuit of course. This is some seriously small soldering and because I don't have a digital microscope handy there will be blurriness. But you'll get the idea.
You have 3 options to disable efuses:
1) Remove the R6T3 resistor. It's a 10k resistor almost eyelash size on the underside of the motherboard. It can be tough to remove as you will have to heat both sides simultaneously. I used to do this, now I go for one of the other ways below
2) If U6T1 is installed, and it is in the above picture, you can bridge the second and third pins where U6T2 is labelled (circled with the blue arrow).
3) If U6T2 is installed, you can bridge the same pins where U6T1 is installed in the picture. Bridge the same pins, (i.e. the bottom right and bottom middle pin).
Once that's done and tested with a multimeter, reassemble and enjoy your JTAG 0
0 -
Xbox Live?
NO. The dashboard patches that make it possible to run unsigned code (homebrew) are easily detectable. It won't be long before you get banned. And why needlessly waste the keyvault? If your JTAG breaks you could sell the keyvault off it to people who were banned from xbox live, or you could unban a console with the keyvault from your JTAG console. I'm not suggesting you do this, I'm just using this to illustrate the point that connecting your JTAG to XBL is shooting yourself in the foot.
Backups?
NO. The JTAG does not allow you to run games burned onto DVD-R media.
So I've been JTAG'd, what now?
Well you can install any 2.5" hard drive you like into an enclosure (I run a 500GB hard drive) and the console will detect it as a proper hard drive and allow you to use all of it for installing games. The fun really starts when you get tools like XeXMenu which will allow you to run unsigned (homebrew) applications.
To get it on to your hard drive you need a transfer cable to copy the application over to /Partition3/Content/0000000000000000/C0DE9999/ or you can run it from a CD and then use XeXMenu's file manager to copy the application from a USB stick to the right directory.
Once XeXMenu is installed properly (read the instructions) it should appear as a Game Demo in the dashboard. Next thing I'd do is increase the fan speed to 70%, you can find XeX files for doing this on xbins.
Next you should look at alternate dashboards like Freestyle dash, and Quickboot which creates shortcuts to your homebrew applications so you can get to them from the NXE dashboard instead of having to go into NXE, then XeXMenu, find the location of your application with the file manager and then launch your homebrew application.
Maybe even look at dashlaunch which will auto-launch an application (might I suggest freestyle dash) on boot up - win!
And with that, off you go and explore the JTAG
Here are some things which will get you and your jtag off on the right foot.0 -
Assuming your finished, in my opinion thats the best post I've ever seen on this forum. I hope everyone will appreciate the time & effort you put into that, as it really shows. Well done TouchingVirus, fantastic guide :cool:0
-
veeeery nice mate.
can we have it stocked please?0 -
Excellent write up will be using as a guide for all future jtags
 0
0 -
Advertisement
-
Man that is some unbelievable guide. Fair play!!0
-
My thanks to whoever stickied this thread
 0
0 -
Wasn't me, so it must have been WMN. There's a spot in his Console Modding FAQ sticky for a nice 'TouchingVirus' Complete JTAG Tutorial' link to your own thread though
 0
0 -
Just updated the guide a small bit there, referencing the lack of ability to play backups or use xbox live with a JTAG. People probably knew it already, but no harm in having it in the guide.0
-
this is easyer that se7sins thanks tv for helping me out with my xbox i have a 250gb in mine with all my games and doing mw2 lobbies will be gettin the other xbox up to u soon for jtaging.0
-
Advertisement
-
this is easyer that se7sins thanks tv for helping me out with my xbox i have a 250gb in mine with all my games and doing mw2 lobbies will be gettin the other xbox up to u soon for jtaging.
thats why people (I mean developers and hackers) lost interest in Xbox homebrew. Hosting hacked MW2 lobbies to boost your stats in games - is that what we where waiting all those years?0 -
Xellous is taking it's time giving me the Raw Flash how long does this normally take on a Xenon?0
-
What you using LTP or USB i used usb took 15 mins less tv helped me out0
-
I'm connected to the Xbox through firefox and I am attempting to dump the Raw Flash with Xellous0
-
Xellous' HTTP daemon is very basic, and as a result has a few bugs. I've never dumped a nand successfully over it, I always had to do it via the reader.
kevin-46 uses the nand-x and I was blown away by the speed of it, it would do a 16MB Xenon in 2 minutes or less. I'm half thinking of investing in one myself 0
0 -
-
Ok xbox disassembled, the jtag bits and bobs I ordered should arrive tommorrow or Fri at the latest.

Quick Q, is it worth taking the heatsink off and applying some Artic Silver while I have it in bits?0 -
on a jasper? Personally i wouldnt bother0
-
-
TouchingVirus wrote: »Xbox Live?
NO. The dashboard patches that make it possible to run unsigned code (homebrew) are easily detectable. It won't be long before you get banned. And why needlessly waste the keyvault? If your JTAG breaks you could sell the keyvault off it to people who were banned from xbox live, or you could unban a console with the keyvault from your JTAG console. I'm not suggesting you do this, I'm just using this to illustrate the point that connecting your JTAG to XBL is shooting yourself in the foot.
Backups?
NO. The JTAG does not allow you to run games burned onto DVD-R media.
So I've been JTAG'd, what now?
Well you can install any 2.5" hard drive you like into an enclosure (I run a 500GB hard drive) and the console will detect it as a proper hard drive and allow you to use all of it for installing games. The fun really starts when you get tools like XeXMenu which will allow you to run unsigned (homebrew) applications.
To get it on to your hard drive you need a transfer cable to copy the application over to /Partition3/Content/0000000000000000/C0DE9999/ or you can run it from a CD and then use XeXMenu's file manager to copy the application from a USB stick to the right directory.
Once XeXMenu is installed properly (read the instructions) it should appear as a Game Demo in the dashboard. Next thing I'd do is increase the fan speed to 70%, you can find XeX files for doing this on xbins.
Next you should look at alternate dashboards like Freestyle dash, and Quickboot which creates shortcuts to your homebrew applications so you can get to them from the NXE dashboard instead of having to go into NXE, then XeXMenu, find the location of your application with the file manager and then launch your homebrew application.
Maybe even look at dashlaunch which will auto-launch an application (might I suggest freestyle dash) on boot up - win!
And with that, off you go and explore the JTAG
Creating a JTAG is against Microsoft policy and its not a case of if you get caught more like when you get caught adn when you do, you will be banned:cool:.0 -
Advertisement
-
-
It says that very clearly in what you quoted, not sure what point you are trying to make.
point is if you have a JTAG you'll get banned....plain and simple. Also i work for Xbox Support so if theres any gamertags on this thread i will personally send them to the enforcement team to be investigated0 -
point is if you have a JTAG you'll get banned....plain and simple. Also i work for Xbox Support so if theres any gamertags on this thread i will personally send them to the enforcement team to be investigated
And thats clearly stated in the OP's guide.Xbox Live?
NO. The dashboard patches that make it possible to run unsigned code (homebrew) are easily detectable. It won't be long before you get banned.
Typically its 4-5 hours before you are banned.0 -
-
Overtimer,
I do not appreciate threats to the members of the forum I moderate. I'm temporarily banning you from Console Modding For either bullying or trolling (take your pick). Myself and the other mods will review the ban and get back to you.
Witnessmenow
FYI this is what i had the issue withAlso i work for Xbox Support so if theres any gamertags on this thread i will personally send them to the enforcement team to be investigated0 -
Creating a JTAG is against Microsoft policy and its not a case of if you get caught more like when you get caught adn when you do, you will be banned:cool:.
I'm sorry, but if you're going to represent an official stance on this, at least make it correct.
Modifying any part of the console or it's software is strictly against the terms of use of Microsoft Xbox live. It is not against Microsoft policy to JTAG your console, it's against Xbox Live's policy to use it on Live because it's modified. Microsoft have no say in what you do with your own console as long as you keep it off Live.
Threats mean nothing as anybody with half a brain wouldn't use a JTAG on XBL anyways. Also, in my opinion it really isn't any of your business who does what here - you're not part of the enforcement team, you're only frontline support. You should spend less time trying to drum up kudos from your boss for wasting the enforcement team's time, and more time supporting the people you're meant to support - i.e XBL Customers.
You're more than welcome to investigate my gamertag, any console it has popped on to the Live network with in the last year has been untouched - I suspect that's the case for most users here. As an added point, none of my JTAGs get a sniff of the internet so best of luck banning the consoles you don't even know I have :pac:
Now please, I'm going to have to ask you to take your trolling somewhere else. This is a guide, not a witch hunt.0 -
you tell him tv aha0
-
Asshole get a lifeyou tell him tv aha
Even though Overtimer was trolling, it doesn not mean we can personally abuse him Kevin. He is still a boards member & we are all still bound by the rules, despite his lack of candour. Please refrain from doing it
Now, I'm not about to watch TV's awesome thread be ruined by bickering & whatnot, so back to the jtag talk folks :cool:0 -
Well said tv overtimer would want to put some overtime in with Microsoft he must have it very easy if he is able to sit on boards and make idle threats0
-
Advertisement
-
Well said tv overtimer would want to put some overtime in with Microsoft he must have it very easy if he is able to sit on boards and make idle threats
Wittnesmenow is dealing with the issue. TV went to the time & trouble to create us a complete & thorough guide on jtagging an xbox360, out of respect for that lets not fill it up with off topic posts.
Incase my earlier comment wasn't clear enough, keep on topic from here on out.0 -
Ya'll gonna get banned lads . Permanently0
-
Xbox_Employee wrote: »Ya'll gonna get banned lads . Permanently
Sure, If you bring it online only haha0 -
-
Can I just add in a note here about the Nand-X.
The nand-x is superfast - it dumps the first 1000 blocks (roughly 64mb) of the arcade in a shade under 9 minutes as opposed to 24 for my PIC reader. However, the Nand-x is using a different wiring method for the JTAG, taking a feed from the ROL (Ring of Light) on the wifi board. I do not suggest using the Nand-X QSBs for the JTAG part unless you have a Xenon.
So follow the Nand-X install instructions to the letter if you have a Xenon. If you do not have a Xenon, follow the Nand-X instructions and use QSBs for soldering J1D2 and J2B1, but use the transistor method outlined above for the JTAG part of the soldering.0 -
Whats the diff between JasperBB.xellous.smc and Jasper.xellous.smc please?0
-
Advertisement
-
JasperBB is for Big-Block jaspers - jasper's with onboard storage (256/512MB).
I'll tell you the version I went with to get Xellous on your console - this one. Use the Xellous.jasperbb by mana.bin file. And when building freeboot, use the SMC file from that ZIP too .
.
If you own a Big-Block Jasper, I always start off with that file and not the JasperBB from the archive with multiple files which can have issues with certain Jaspers 0
0 -
I am having a bit of trouble with my nand-x. I managed to do 3 full 60mb odd nand dumps, but between the 2nd and the 3rd I got a Could not detect a Flash controller error. I rebooted the PC (Win 7) and it went away, all 3 dumps match. I then dumped the Keyvault 3 times all matching but the error came back between the 2nd and the 3rd, I had lunch, came back and it was working again.
Anyways I then flashed the xellous.jasper.smc and my keyvault, but now I realise thanks to your reply thats the wrong file. Now all I get is the error, I also tried an XP laptop.
Any ideas please?
For context the only thing I have done since flashing the xellous.jasper.smc was put the mobo back in the case and connect the fan and light ring, and plug in the AV cable. I wouldnt think any of those would cause issues but I am no expert
Is it possible I cracked one of the nand dump QSB points when removing the cables from the QSB? The thing that makes me think this is not the case is that I initially experienced the issue in between successful dumps and writes.0 -
Sometimes something happens with nandpro or the reader that a reboot or a restarting of the command line console fixes. I have a batch file that dumps a nand 5 times, it's just 5 commands. But no matter what reader I run it with, nandpro will dump 1, 3 and 5 just fine and complain about no flash controller or incompatible ARM hardware on dumps 2 and 4 - it's a funny old thing but I wouldn't read too much into it.
You flashed the SMC file to the start of the nand? That shouldn't really break anything, it's just like flashing a bad dump
If you've got a multimeter handy you can multimeter from the J1D2 and J2B1 points on the underside of the board to the pin headers on the QSBs to test. If there are broken points then try to repair them. But definitely the first thing is a multimeter continuity test on all points 0
0 -
Ah continuity, the check of the gods
 I use it for nearly everything modding related. 0
I use it for nearly everything modding related. 0 -
TouchingVirus wrote: »Sometimes something happens with nandpro or the reader that a reboot or a restarting of the command line console fixes. I have a batch file that dumps a nand 5 times, it's just 5 commands. But no matter what reader I run it with, nandpro will dump 1, 3 and 5 just fine and complain about no flash controller or incompatible ARM hardware on dumps 2 and 4 - it's a funny old thing but I wouldn't read too much into it.
You flashed the SMC file to the start of the nand? That shouldn't really break anything, it's just like flashing a bad dump
If you've got a multimeter handy you can multimeter from the J1D2 and J2B1 points on the underside of the board to the pin headers on the QSBs to test. If there are broken points then try to repair them. But definitely the first thing is a multimeter continuity test on all points
Thanks TouchingVirus, I'll nab a multimeter tomorrow and check them. I have tried many times since and am having no joy, I have abandoned proceedings for the evening. 0
0 -
Advertisement
-
Build Instructions:
For simplicity you need the following:
1) Your CPU Key
2) Your Freeboot v0.032 (Dash 9199) nand file and SMC
3) 12611.zip (xbins)
4) fbBuild v0.1 (xbins)
Getting ready
Download fbBuild and extract it to a folder - say C:\fbBuild
Download 12611.zip and extract the contents to C:\fbBuild\data
Edit C:\fbBuild\1blkey.txt. On the first line is a dummy key - replace it with DD88AD0C9ED669E7B56794FB68563EFA
Edit C:\fbBuild\mydata\cpukey.txt. On the first line is a dummy key - replace it with the CPU key of the console.
Extracting KV and SMC_CONFIG.bin
Open up 360 Flash Tool v0.97 and click Settings->Options. Tick the box that says "Extract ibuild compatible files". Then open your freeboot nand and click extract on the bottom. Tick the box for 'config blocks' and 'Keyvault' and click OK. Choose a folder for these files. When extraction is done, go to that folder and there'll be a folder called freeBOOT, click into it, then into data and you will find two files - kv.bin and smc_config.bin. Copy these two files to C:\fbBuild\mydata
Picking the right SMC (not for Xenon consoles)
This step is very important if your console is not a xenon - flashing the wrong SMC can end your JTAG When you built freeboot v0.032 you probably downloaded some pre-built Xellous files and SMC files from the guide:
When you built freeboot v0.032 you probably downloaded some pre-built Xellous files and SMC files from the guide:
Zephyr, Jasper, Falcon
Jasper Big Block Alternative
Well each of these files had an SMC in the archive and when building your custom freeBOOT using Bestpig's tool you renamed the file to smc.bin and copied it into data directory. This is the right SMC for your console, so once again rename it to smc.bin and copy it to C:\fbBuild\mydata
Build freeBOOT
Open a command prompt, go to C:\fbBuild and type the followingfbbuild -c <model> -d mydata updflash.bin
<model> is either xenon, falcon, zephyr, jasper, jasper256, jasper512
Freeboot v0.04 will build as updflash.bin - copy it to USB, boot to Xellous and flash it.
Post-Install
Download the full system update - http://download.microsoft.com/download/4/1/D/41D9A2BA-3B48-4BD5-B613-122E7C3A1390/SystemUpdate12611.zip
Extract to a USB stick (blank)
Insert USB stick into console
Power console on, accept the update, the console will apply and then reboot.
If you had modified the console fanspeed on the previous dash (I run at 60% on the Jaspers) then run FanSpeed_60.xex or whatever via XeXMenu 0
0 -
As reported by justryan in a separate thread, you no longer need to build freeBOOT v0.04 yourself with fbBuild - Bestpig has kindly updated his freeBOOT Toolbox so just follow the guide as it was originally in the first 3 posts and you're laughing again - all together now, MUAHAHAHAHAH
 0
0 -
Bestpig FTW!
 0
0 -
So I realise my third post-JTAG post was very short, I was tired of writing up, but here is a more detailed post about what to do after you have a JTAG. Keep in mind this is not exhaustive and doesn't touch on emulators, mainly because I have not tried emulation on my own JTAG

The Hard Drive
The first thing you'll need to properly take advantage is a hard drive, but because you have a JTAG it can be any hard drive you like as long as it's a 2.5" SATA hard drive. You can pick up a third-party enclosure on DealExtreme for $9.90 with free shipping, then just pop any hard drive into it, say this 250GB one from Amazon.co.uk. Total cost for the 250GB is less than you would pay in a shop for the same drive.
An advantage for picking the 250GB WD drive (WD2500BEVT) is that you can turn it into an "official" hard drive if you want by using the tool HDDHackr. The hard drive will then also work between JTAGs and official consoles, even though your JTAG-related programs won't. Personally, I bought a 500GB hard drive for the JTAG, and use a 120GB on my other, virgin console. My housemate swaps his 120GB from virgin to JTAG with ease though
XeXMenu
For this you don't need a hard drive as it's a small application but it is vital to get you up and running. XeXMenu is a filesystem manager that enables you to run .xex files, FTP stuff to your hard drive, copy files from USB hard drives/sticks (FAT32 only) and a few other things. It's the first step. You need to download the XeXMenu v1.1 file that can be found on xbins.org in /XBOX 360/Dashboards/XeXMenu and burn the ISO file in that archiveTo download from Xbins you can get an application called autoxbins, or open up mibbit.com or the IRC client of your choice, connect to EFNET as your username, join #xbins and type !list in the chatroom. You will be PM'd from the bot, who will tell you you can access the xbins FTP server and will give you the address, username and password. Then use an FTP client to connect and get your stuff. When you disconnect, type !list again to re-active your account. Do not spam !list, you'll get banned from the chatroom for 15 minutes.
Once you have burned XeXMenu, throw it into the console and play it. The objective here is to go to the DVD drive, and copy the C0DE9999 folder to your MemoryUnit or Hard Drive's /Content/0000000000000000/ folder. The first screen you land on is the "Games Discovery" page, use RB/LB to change to Configuration and change the skin to RetroNintendo (easiest screen to see what's going on, and it's awesome ). Then change to the Filesystem screen. To change device, press X and choose a device (DVD: is what you're looking for). Highligh C0DE9999 and press Y, and then A on copy. Then use X to change to HDD1: or MU: and hit A to go into the content folder, then A to go into the folder 0000000000000000 then hit Y and select paste. C0DE9999 should be copied into the hard drive or internal memory then.
). Then change to the Filesystem screen. To change device, press X and choose a device (DVD: is what you're looking for). Highligh C0DE9999 and press Y, and then A on copy. Then use X to change to HDD1: or MU: and hit A to go into the content folder, then A to go into the folder 0000000000000000 then hit Y and select paste. C0DE9999 should be copied into the hard drive or internal memory then.
Go back to the dashboard, go to Games Library -> Demos and XeXMenu v1.1 should be there. This is how you now launch XeXMenu, so you can remove the CD and keep it safe
Good Apps
NXE2GOD v1.1 - NXE to GOD converts games you have installed to the Hard Drive (a proper one, not a USB one with 16GB in use) to Games-on-Demand. So take your original, install to the hard drive, and run NXE2GOD and put your disc away. In order to change the game to a GOD, the whole thing becomes "unsigned". The essence of the JTAG is it doesn't care if content is signed or unsigned, but all other consoles do, so you won't be able to play the games on a non-JTAG console. You can download this from Xbins or MegaUpload or wherever. Once again, use XeXMenu to FTP it to your hard drive or copy the application from a USB stick and put it in the /Content/0000000000000000/C0DE9999/008000/ folder. There will already be an application in there starting with C0DE9999 - that's XeXMenu, so leave it alone You run NXE2GOD the same way you run XeXMenu - via the Game Demos in the Game Library of the Dashboard.
You run NXE2GOD the same way you run XeXMenu - via the Game Demos in the Game Library of the Dashboard.
ISO2GOD - If you have game ISOs, this Windows program will attempt to convert them to GOD folders on your hard drive. After which you can FTP or copy to a USB stick (a big one >8GB to be safe, FAT32) or a USB hard drive (FAT32) using XeXMenu. Unlike the apps, you don't put these into the C0DE9999 folder, you drop them right into /Content/0000000000000000/ - There are some reports it isn't working with the latest AP2.5 games, if true then I expect a fix soon
FanSpeed - A set of XEX files that change the fanspeed of the 360 from Auto (which I think is too low) to a set percentage of MAXSPEED. I run the 60% one for best noise/cooling tradeoff, even on my jasper. You stick it on a USB stick, start XeXMenu, navigate to the USB stick, highlight FanSpeed_60.xex and press A to run it - you don't copy it to the hard drive, it isn't that type of application, you need to run it from XeXMenu. After the screen goes black and kicks you to the dashboard, reboot the console This is available on xbins and other filesharing sites. You only need to run it once unless you update your reflash the console or intend on changing the speed.
This is available on xbins and other filesharing sites. You only need to run it once unless you update your reflash the console or intend on changing the speed.
XM360 - So you have two consoles, one of which has all your purchased arcade titles. You can't play them on your JTAG, because then you need to sign in to Live, which we know is a big no-no on JTAGs. If you stick in your hard drive you'll see all the games are trial versions and you're disappointed. Well XM360 is for you. If you have XeXMenu installed on internal memory, stick the hard drive with the arcade games in and fire up XeXMenu. If you do not have XeXMenu on an internal memory unit, you can run it from the CD if it isn't on the hard drive with the arcade titles Put a big USB stick or hard drive into a USB slot too with XM360 on it.
Put a big USB stick or hard drive into a USB slot too with XM360 on it.
Now you're in XeXMenu, copy the Arcade title folders from HDD:/Content/0000000000000000/<TITLEID> to the USB stick. There'll probably be a good few folders in there, some relating to full games, some relating to the arcade games. If you know what you want, you can look up that game's TitleID on Google - e.g. Splosion Man is 5841098F.
So now that they're copied to the USB Stick, turn off the console, remove the hard drive and put in your JTAG hard drive. Copy the folders back to /Content/0000000000000000/ and then copy the XM360 folder to anywhere on the hard drive you like, I put it in the root folder as /XM360/ because I hate having to navigate all the way down to C0DE9999 - there's no need to because you have to run XM360 through XeXMenu so make it easier for yourself Run XM360, and it will scan the hard drive for titles. You can then use it to unlock the titles, allowing you to play the full versions that you paid for on your JTAG without having to sign in to Xbox Live!
Run XM360, and it will scan the hard drive for titles. You can then use it to unlock the titles, allowing you to play the full versions that you paid for on your JTAG without having to sign in to Xbox Live!
A comprehensive (I don't know if complete) TitleID list is available at http://360.kingla.com/
Freestyle Dash - The mother of replacement dashboards. It's an alternative dashboard to NXE, has many themes, it's own FTP server and is generally cool. I started this thread because I was taken aback at how pretty the skin I found was You can get it on Xbins, and put it anywhere on the hard drive you like. I put mine into the C0DE9999 folder but I made a folder in there called 0700 (there's another one in there 008000, but that's not it) so FSD shows up in the Games Library and I can launch it right from NXE without going through XeXMenu.
You can get it on Xbins, and put it anywhere on the hard drive you like. I put mine into the C0DE9999 folder but I made a folder in there called 0700 (there's another one in there 008000, but that's not it) so FSD shows up in the Games Library and I can launch it right from NXE without going through XeXMenu.
If you run the FSD Updater from your PC and connect to your console over FTP it will re-scan your hard drive, scrape websites for pictures and game information and is like XBMC for Games If you don't want to FTP, you can use a Transfer Cable to hook up your hard drive to the computer and FSD Updater will work that way too.
If you don't want to FTP, you can use a Transfer Cable to hook up your hard drive to the computer and FSD Updater will work that way too.
It has an emulator section, which I think searches for XEX files in /EMULATORS/ and other sections I never fully got to grips with. I know v2 of FSD is coming at some stage which is intended to be so much more awesome than the current version, but I think the current version deserves a look
Dashlaunch - Available on xbins, this is an xex file and an .ini file. Run the XEX from XeXMenu and when you start your console it will read the ini file (which you put in the root of your hard drive) and attempt to run the XeX file you specify in the INI file. I pointed my ini file to Freestyle Dashboard, so it auto-launched when I turned on my console
Quickboot - Have you got a pain in the face going into XeXMenu to run your XEX files? Quickboot creates "wrappers" for your XEX files so you can launch then straight from the NXE dashboard after you put the file it generates into C0DE9999/00800 like NXE2GOD. I'm not sure how it works, but I have been meaning to test it out
Edit: Mods - could I get this post linked to in my 3rd post at the start of the thread? Thanks0 -
Using Flash360, I dumped my existing freeBOOT 9199 nand image. Then using BestPig's latest image builder, I punched in my cpu key, selected the output as updflash.bin, opened the newly dumped 9199 bin file, & built the 12611 updflash from that.
Back again to flash360, I selected the updflash file & to discard the current config. KV mismatch error, & nand Zero Paired error, the consensus online is to generally ignore these errors, as I lip-bitingly did. Flash completed, power cycle, hello 12611 :cool:
Why anyone takes the hard way with this I don't understand. BestPig or No Pig! Heading off the MS now for the avatar updates etc.
Heading off the MS now for the avatar updates etc.
Edit - Strangely enough, my fanspeed patched xex seems to have survived the flash process. I thought this part of the nand would be overwritten, requiring fan speed to be patched again but seemingly not in this case.0 -
No, it's not strange

Running the fanspeed patch modifies the config.bin - a lot of people are not taking "live" dumps of their current in-use nand, but are taking the config from the 9199 dashboard updflash.bin they generated the last time BestPig's tool was used - this would be unmodified by the Fanspeed patches so that's why they would have to re-run the patch to modify config.bin
On the other hand, you took your modified (live) config.bin and rammed it through bestpig's tool, no need for a patch :P0 -
TouchingVirus wrote: »No, it's not strange

Running the fanspeed patch modifies the config.bin - a lot of people are not taking "live" dumps of their current in-use nand, but are taking the config from the 9199 dashboard updflash.bin they generated the last time BestPig's tool was used - this would be unmodified by the Fanspeed patches so that's why they would have to re-run the patch to modify config.bin
On the other hand, you took your modified (live) config.bin and rammed it through bestpig's tool, no need for a patch :P
Yes, I am dumb :D 0
:D 0 -
If you get an e71 or e72 error after the avatar update that's normal just power cycle and you'll have avatars0
-
If you get an e71 or e72 error after the avatar update that's normal just power cycle and you'll have avatars
Avatar update ran fine, no eXX's. I've kept my 9199 updflash bin anyhow, suppose it could come in handy at some stage - hopefully not though. As of now, 12611 is doing everything 9199 was doing, 3.5" hdd/no dvd drive included so I'm a happy camper for the mo'.0 -
For some high resolution pictures of a JTAG install on a Jasper (the same for non-Xenon boards) see http://boards.ie/vbulletin/showthread.php?t=20561095590
-
Advertisement
Advertisement
